Protecting a mega industrial facility from fire is not the same challenge as protecting a single building. A large oil refinery, pharmaceutical campus, or integrated manufacturing complex may span hundreds of hectares, house thousands of workers across multiple shifts, and run continuous, mission-critical operations around the clock. A single fire event or worse, a mismanaged alarm response, can trigger cascading shutdowns, endanger lives and cost tens of millions in recovery.
Yet many large industrial facilities still rely on fire alarm architectures that were not designed for this level of complexity. When every detector and device funnels back to one central panel, the system becomes both a reliability bottleneck and a liability. A single communication fault can render the entire fire alarm network non-functional. A nuisance alarm in one zone can disrupt operations across the entire site.
Fire alarm network segmentation is the engineering answer to this problem. By dividing a large, interconnected fire detection and alarm infrastructure into logical, independently managed segments, industrial facilities gain fault isolation, faster emergency response, better scalability, and stronger compliance posture without sacrificing system-wide visibility.
This article provides a detailed, technically grounded explanation of fire alarm network segmentation strategies for mega industrial environments, including deployment frameworks, practical examples, and future-ready design principles.
What Is Fire Alarm Network Segmentation?
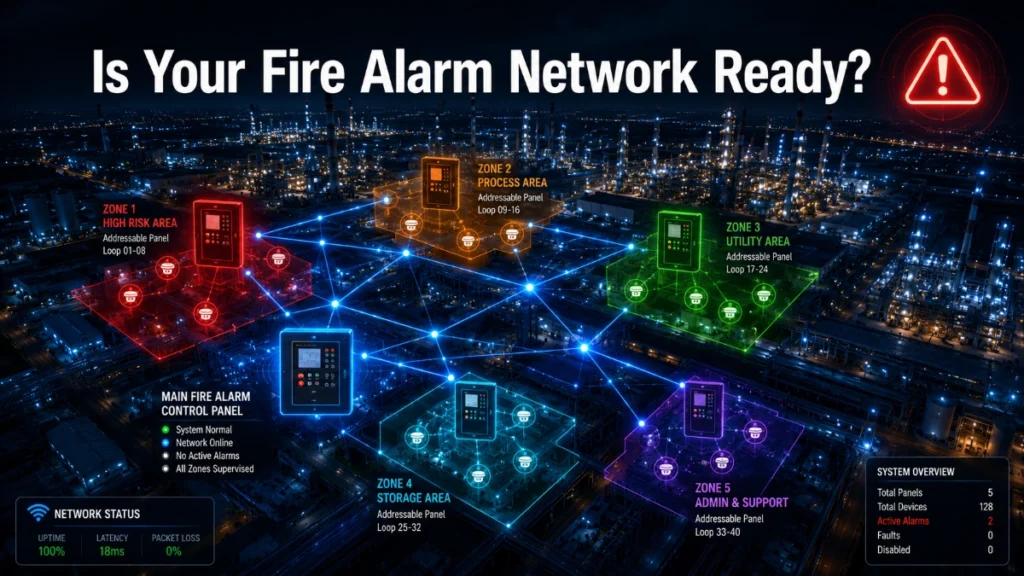
Fire alarm network segmentation refers to the deliberate architectural practice of dividing a large fire detection and alarm system into smaller, functionally independent sections called segments that can operate, communicate, and respond to events autonomously, while still being monitored and coordinated from a central command level.
In a segmented fire alarm infrastructure, each segment is assigned its own control logic, communication pathway, and alarm management capability. A fault in one segment does not cascade across the network. An alarm in one area triggers a precise, targeted response, not a site-wide event. Maintenance on one segment does not require full system downtime.
Segmentation can be applied at multiple levels: physical zones, buildings, process areas, risk categories, communication networks, or command hierarchies. The most effective industrial deployments combine several of these approaches simultaneously.
Modern segmented systems typically rely on addressable fire alarm panels as the distributed control nodes, connected via fibre-optic or redundant communication loops, and managed through intelligent gateway integrations with building management systems (BMS) or industrial SCADA platforms.
How Traditional Fire Alarm Architectures Operate and Where They Fall Short
A conventional fire alarm panel works on a straightforward principle: detectors are wired in zones, and any activated zone triggers an alarm at the central panel. This architecture is simple, proven, and cost-effective for smaller installations.
In mega industrial facilities, however, this centralised model creates serious structural vulnerabilities:
- A single communication failure can disable the entire network.
- All alarm events, from a minor maintenance alert to a serious fire, receive the same level of response urgency.
- Adding new buildings or process areas requires reworking the central panel infrastructure.
- Fault diagnostics require tracing issues across long cable runs to a single panel.
- Emergency response teams receive undifferentiated alarm data, slowing decision-making.
Even addressable fire alarm systems, when deployed in a flat (non-segmented) topology, can suffer from these limitations if they are not architecturally divided. Segmentation is therefore a design philosophy, not just a hardware choice.
Segmentation Approaches for Mega Industrial Fire Alarm Networks
Effective fire alarm network segmentation for large industrial environments draws from a range of proven architectural strategies. Each approach addresses different operational and risk requirements.
1. Zone-Based Segmentation
Zone-based segmentation assigns detectors and devices to defined geographic or functional zones within a facility. Each zone operates with its own alarm logic and can be evacuated or isolated independently. This is the foundational layer of any segmented fire alarm network and forms the basis of compliance with standards like NFPA 72 and BS 5839.
2. Building-Level Segmentation
For multi-building industrial campuses such as integrated petrochemical complexes or pharmaceutical manufacturing parks, each building or structure is treated as an independent fire alarm domain. A dedicated addressable fire alarm panel manages each building, with communication links to a site-level monitoring station.
3. Process-Area Segmentation
In oil and gas facilities, refineries, and chemical plants, specific process areas carry dramatically different fire risk profiles. Compressor stations, distillation columns, storage tank farms, and utility substations each require tailored detection strategies. Process-area segmentation ensures that the alarm logic, detector types (conventional detectors or addressable detectors), and response protocols are precisely calibrated to each zone’s hazard classification.
4. Risk-Category Segmentation
Not all fire risks are equal. Risk-category segmentation assigns fire network segments based on hazard severity from low-risk administrative areas to high-risk flammable storage zones. Each category operates under a different alarm escalation protocol and emergency response priority.
5. Redundant Loop Architecture
In a redundant loop design, each fire alarm segment communicates via a closed loop rather than a single linear cable run. If the loop is broken at any point, communication continues in the opposite direction. This architecture is especially critical in facilities where cable damage from process activity or structural events is a realistic risk.
6. Distributed Control Panel Architecture
Rather than relying on one central panel, a distributed architecture places addressable fire alarm panels at strategic locations across the site. Each panel manages its local segment independently and reports to a supervisory command station. The GST fire alarm system and similar intelligent platforms support this model effectively.
7. Fibre-Optic Network Segmentation
Fibre-optic communication links offer immunity to electromagnetic interference, a critical advantage in industrial environments with heavy machinery and electrical systems. Segmenting fire alarm communication networks over dedicated fibre-optic backbones dramatically improves signal integrity, communication speed, and resilience.
8. Intelligent Gateway Integration
Intelligent gateways serve as translation and coordination layers between fire alarm segments, BMS platforms, and SCADA systems. They ensure that alarm data from different segments is normalised, prioritised, and routed to the correct response teams without data overload at the command centre.
9. Hierarchical Command Structures
A hierarchical segmentation model organises the fire alarm network into tiers: device-level, segment-level, building-level, and site-level. Each tier handles its own alarm processing and escalates only significant events upward. This structure prevents alarm flooding and keeps emergency response teams focused on actionable intelligence.
10. Edge Processing Segmentation
Edge processing places computational intelligence at the panel or gateway level, rather than relying entirely on a central server for alarm analysis. Each segment processes its own data locally, enabling faster alarm decisions and reducing dependence on network connectivity.
11. Fail-Safe Communication Pathways
Segmented networks include dedicated fail-safe communication pathways, redundant radio, fibre, or hardwired channels that activate automatically if primary communication links fail. This ensures that every segment remains connected to emergency monitoring at all times.
12. Segmented Evacuation Control Logic
Rather than triggering a site-wide evacuation for every alarm, segmented evacuation logic initiates targeted responses based on the specific segment that has activated. This reduces unnecessary disruption, prevents panic-related injuries, and directs emergency responders to the precise location of concern.
How Segmentation Improves Industrial Fire Alarm Performance
Fault Isolation
When a communication fault, power issue, or device failure occurs, segmentation ensures it stays contained within one network segment. The rest of the facility continues to operate under full fire protection. In a flat architecture, the same fault could compromise the entire system.
Emergency Response Coordination
Segmented systems provide emergency response teams with precise, actionable alarm data. Instead of receiving a generic “Zone 4 alarm” notification, operators see exactly which detector in which segment has activated, along with its process-area context and risk category, dramatically accelerating response decisions.
System Scalability
Industrial facilities grow. New production lines, warehouses, and utility areas are added over time. A segmented fire alarm infrastructure accommodates expansion by adding new panels and segments to the network without redesigning the existing architecture.
Maintenance Efficiency
Segment-level maintenance can be performed without taking the entire fire alarm system offline. Engineers can isolate a specific panel or loop for testing, firmware updates, or device replacement while adjacent segments remain fully operational.
Network Resilience
With redundant loops, multiple communication pathways, and edge processing at each segment, segmented networks are inherently more resilient. They continue to function even when individual components fail.
Alarm Prioritization
Intelligent segmentation supports multi-level alarm prioritisation. A smoke alarm in an administrative office and a fire detection event near a high-pressure gas line require very different responses. Segmented logic ensures each receives the appropriate priority level.
Regulatory Compliance
Standards such as NFPA 72, BS 5839-1, EN 54, and local industrial fire codes increasingly require documented fault isolation, zone-level accountability, and independent verification of alarm integrity. Segmented architectures are purpose-built to satisfy these requirements.
Cybersecurity Posture
In connected industrial environments, fire alarm networks that communicate with BMS or SCADA systems represent a potential cybersecurity surface. Segmentation limits lateral movement within the network; a compromise in one segment does not automatically expose the rest of the fire alarm infrastructure.
Operational Continuity
Unnecessary full-site shutdowns from a single alarm event can cost industrial facilities millions of dollars per hour. Segmented evacuation logic and alarm prioritisation ensure that operations continue in unaffected areas while the actual incident is addressed.
Practical Deployment Examples Across Industrial Sectors
Oil & Gas Facilities and Refineries
Refineries deploy process-area segmentation to isolate distillation, fracking, storage, and utility zones. Redundant fibre-optic loops connect distributed addressable fire alarm panels across vast outdoor sites, with intelligent gateways integrating into plant SCADA systems.
Manufacturing Plants
Large assembly plants use building-level and process-area segmentation to separate raw material storage, production lines, finishing areas, and dispatch zones. Each zone carries its own risk profile and evacuation protocol.
Power Generation Plants
Power plants segment turbine halls, control rooms, fuel storage areas, and cooling systems independently. Fail-safe communication pathways ensure that even a major electrical event in one segment does not compromise alarm monitoring in adjacent areas.
Airports and Logistics Hubs
Airports deploy hierarchical segmentation across terminals, cargo warehouses, baggage systems, fuel storage, and aircraft hangars. Segmented evacuation logic enables targeted passenger management without requiring full terminal evacuations for localised alarms.
Data Centers
Data centres use high-precision addressable detectors with process-area segmentation to protect server halls, cooling infrastructure, UPS rooms, and cable management areas independently. Gas suppression systems are integrated with segment-level fire alarm logic to prevent collateral damage.
Pharmaceutical Facilities
Pharmaceutical manufacturers deploy risk-category segmentation to separate cleanroom environments, chemical storage, utility areas, and laboratories. Cleanrooms carry specific alarm protocols that minimise contamination risk during emergency response.
Smart Industrial Parks and Warehouse Campuses
Large logistics and smart industrial parks use building-level segmentation with intelligent gateway integration, enabling a single operations centre to monitor hundreds of individual fire alarm segments across multiple structures in real time.
Common Failures in Poorly Segmented Fire Alarm Networks
Understanding what goes wrong in unsegmented or poorly designed fire alarm networks reinforces why structured segmentation is an operational imperative, not just a design preference.
- Single-point communication failures that disable fire detection across an entire facility.
- Alarm flooding occurs when minor nuisance alarms overwhelm operators and mask genuine fire events.
- Inability to isolate a faulty detector without shutting down the entire fire alarm system.
- Delayed emergency response due to imprecise alarm location data.
- Failed regulatory audits due to the inability to demonstrate zone-level alarm integrity.
- Cybersecurity breaches are propagating across an unsegmented fire alarm network connected to BMS.
- Unnecessary full-site evacuations triggered by localised events disrupting production and causing injury risk.
- System scalability failures when new buildings or process areas cannot be integrated without a full redesign.
- Communication path dependency on a single cable run that passes through a high-risk area.
Each of these failures represents both an operational and a safety risk, and each is directly mitigated by a well-designed fire alarm network segmentation.
How Intelligent Segmentation Improves Fire Infrastructure Reliability
Intelligent segmentation moves beyond simply dividing the network into zones. It introduces active, automated management of fire alarm segments through technology-driven logic.
Key features of intelligent segmentation include:
- Automatic fault detection and segment isolation without operator intervention.
- Dynamic alarm routing based on real-time segment status and risk level.
- Integration with building automation systems for automated door closure, HVAC isolation, and suppression activation.
- Event logging at the segment level for post-incident forensic analysis and audit trails.
- Remote diagnostic access, allowing fire system engineers to assess segment health without being physically present on-site.
- Predictive maintenance alerts based on device performance trends within each segment.
Platforms built on the GST fire alarm system architecture, as well as other intelligent fire infrastructure solutions, are specifically designed to support these capabilities at scale. The combination of addressable fire alarm panels, distributed control, and intelligent communication gateways creates a fire safety ecosystem that actively manages its own reliability.
Comparison: Flat Centralised vs Segmented Intelligent Fire Alarm Architecture
| Criteria | Flat Centralised Architecture | Segmented Intelligent Architecture |
| Architecture Type | Flat Centralised Architecture | Segmented Intelligent Architecture |
| Fault Isolation | Single point of failure affects entire network | Faults isolated to individual segments |
| Scalability | Limited — adding devices strains the main panel | Highly scalable with distributed panels and gateways |
| Alarm Prioritization | Basic zone-level alarming only | Intelligent multi-level alarm triage and prioritisation |
| Maintenance | Requires system-wide shutdown for major work | Segment-level maintenance without full system downtime |
| Emergency Response | Centralised evacuation logic only | Segmented, zone-specific evacuation control logic |
| Cybersecurity | Flat network = larger attack surface | Segmented network reduces lateral threat movement |
| Regulatory Compliance | May struggle in complex multi-zone environments | Designed for compliance across diverse risk zones |
| BMS Integration | Limited integration capability | Full integration with BMS, SCADA, and automation systems |
| Redundancy | Limited or no path redundancy | Redundant loop architecture with failsafe pathways |
| Panel Type Best Fit | Conventional fire alarm panel (small sites) | Addressable fire alarm panel (large/complex sites) |
The Future of Fire Alarm Network Segmentation: Intelligent, Connected, and Predictive
AI-Assisted Fire Network Diagnostics
Artificial intelligence platforms are beginning to analyse fire alarm network data in real time, identifying developing faults before they cause failures, detecting unusual alarm patterns that may indicate equipment degradation, and recommending maintenance actions proactively. AI-assisted diagnostics reduce unplanned downtime and strengthen network integrity across large segmented systems.
Cloud-Connected Fire Alarm Ecosystems
Cloud connectivity allows multi-site industrial operators to monitor fire alarm segment health across geographically distributed facilities from a single dashboard. Real-time alarm status, device health metrics, and compliance reports become instantly accessible to remote operations teams.
Digital Twins for Fire Safety
Digital twin technology creates a real-time virtual model of the physical fire alarm network. Engineers can simulate emergency scenarios, test segmentation logic changes, and validate expansion designs against the digital twin before making any changes to the live system.
IoT-Enabled Fire Segmentation
Internet of Things (IoT) platforms extend fire alarm segmentation to include wireless environmental sensors, gas detectors, and thermal imaging devices. These IoT nodes feed segment-level data into the main fire alarm network, increasing detection granularity without adding significant wiring complexity.
Predictive Fault Isolation
Advanced analytics platforms identify which segments, panels, or devices show early indicators of communication degradation or device failure. Predictive fault isolation allows maintenance teams to address problems before they affect alarm performance, shifting the entire fire safety operation from reactive to proactive.
Self-Healing Fire Communication Networks
Self-healing network architectures automatically reroute communication traffic around failed segments or damaged cable runs in real time. When a pathway fails, the network instantly reconfigures to maintain full alarm coverage without any human intervention.
Integration with Building Management Systems and Industrial Automation
A segmented fire alarm network does not operate in isolation. In mega industrial facilities, effective fire safety depends on real-time integration with building management systems, SCADA platforms, access control, CCTV, and emergency communication systems.
Intelligent gateways translate fire alarm segment data into formats compatible with BMS protocols such as BACnet, Modbus, and LonWorks. This integration enables:
- Automatic HVAC shutdown and smoke control activation based on alarm segment.
- Automatic release of fire doors and access barriers.
- Coordination with industrial interlock systems to safely shut down process equipment.
- Real-time fire alarm status visible on the same dashboard as production monitoring systems.
For maintenance teams, segment-level BMS integration provides a unified view of fire alarm system health, enabling faster diagnostics and better-informed maintenance scheduling.
Cybersecurity Considerations in Segmented Fire Alarm Networks
As fire alarm systems become increasingly connected to BMS, cloud platforms, and remote monitoring services, cybersecurity becomes an important design consideration. A segmented fire alarm network inherently limits cybersecurity exposure by containing potential breaches within individual network segments.
Best practices for cybersecurity in industrial fire alarm networks include:
- Implementing network-level firewalls and access controls between fire alarm segments and corporate IT networks.
- Using encrypted communication protocols for all remote monitoring and cloud-connected functions.
- Maintaining separate VLANs or physical network separation between the fire alarm infrastructure and the general facility networks.
- Conducting regular cybersecurity audits of all networked fire alarm components.
- Ensuring that firmware updates for panels and gateways follow a controlled, tested deployment process.
Read Also: Real-Time Fire Event Synchronisation Across Multiple Buildings
Read Also: Identifying Hidden Instability in Fire Detection Infrastructure