In a large commercial tower on the outskirts of a major city, the annual fire safety inspection concluded without a single finding. Every detector responded. Every panel indicator showed green. The system certificate was signed, the report filed, and the building management team moved on.
Three months later, a smouldering electrical fault in a cable tray, the kind that produces slow, low-density smoke before igniting, went undetected for eleven minutes. The detectors in that zone had been accumulating dust for two years. Their sensitivity had drifted below the threshold required to detect early-stage combustion. The system had passed its last test because the test used a standardised smoke quantity far greater than that produced by the slow-burning fault.
The alarm eventually triggered. But the delay allowed the fire to spread through two floor sections before suppression systems activated. No fatalities occurred, but the financial, operational, and legal consequences were severe.
This scenario is not rare. It is a pattern repeated in warehouses, hospitals, data centres, airports, and manufacturing plants worldwide. Fire detection infrastructure develops hidden instability, a gradual, invisible erosion of performance that does not announce itself through visible alarms or obvious system faults. And it is one of the most underaddressed risks in modern fire safety engineering.
This article examines exactly what hidden instability is, why it develops, how it manifests across real-world facilities, and what engineering teams and facility managers can do to identify, audit, and prevent it.
What Is Hidden Instability in Fire Detection Infrastructure?
Hidden instability describes a state in which a fire alarm or detection system functions adequately under normal or test conditions but operates below reliable performance thresholds in real-world or stress conditions. The system does not fail outright. It does not generate fault codes. It passes routine inspections. But its ability to detect fires accurately, quickly, and reliably is compromised.
This is distinct from a system that has already failed. A failed system is visible. A system with hidden instability is dangerous precisely because it is invisible.
Fire detection infrastructure encompasses a wide ecosystem of components:
- Smoke, heat, and multi-criteria detectors.
- Addressable and conventional fire alarm panels.
- Loop wiring and communication circuits.
- Power supplies and backup batteries.
- Relay outputs, cause-and-effect logic engines.
- Integration interfaces with BMS, suppression, and emergency voice systems.
- Network infrastructure in networked or campus-wide systems.
Hidden instability can develop in any of these components, and because they are interdependent, a weakness in one area degrades the performance of the entire system.
Why Instability Often Goes Unnoticed
The primary reason hidden instability escapes detection is simple: conventional fire alarm testing is event-based rather than condition-based. Most inspection regimes confirm that devices respond to a stimulus. They do not continuously measure the quality of that response, the communication integrity of the loop, the health of backup power, or the calibration accuracy of detection algorithms.
Several structural factors allow instability to accumulate undetected:
- Annual or semi-annual inspection schedules create long windows during which performance can degrade between checks.
- Inspection methodologies test for the presence of response, not speed, accuracy, or consistency of response.
- Addressable systems log fault data, but many facilities do not routinely analyse event logs for early warning indicators.
- Third-party system integrators sometimes hand over systems without comprehensive commissioning baselines, making performance drift impossible to measure.
- Maintenance teams are often reactive, responding to alarms and faults rather than proactively investigating marginal performance indicators.
The result is a growing population of fire detection systems operating in a grey zone between full functionality and silent failure.
16 Hidden Instability Factors That Compromise Fire Detection Performance
Understanding where instability originates is the first step toward controlling it. The following factors are the most operationally significant causes of hidden degradation in fire detection infrastructure.
1. Voltage Fluctuation Issues
Fire alarm control panels and addressable detectors operate within defined supply voltage tolerances, typically 18–30V DC. Voltage outside this range causes intermittent communication errors, false sensitivity thresholds, and in severe cases, spontaneous device resets. Electrical noise from HVAC equipment, industrial machinery, or UPS switching cycles creates micro-fluctuations that standard power monitoring does not capture.
In industrial plants and manufacturing facilities, voltage instability is one of the leading causes of unexplained fire alarm faults and is frequently misattributed to detector ageing.
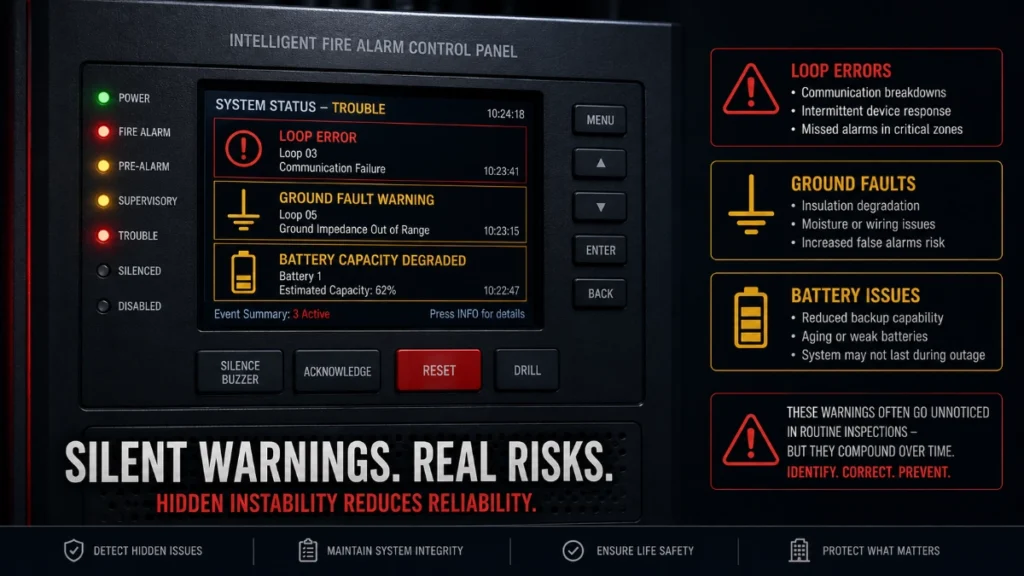
2. Loop Communication Instability
Modern addressable fire alarm panels use supervised communication loops that poll each device at defined intervals. When communication quality degrades due to cable resistance increases, connection corrosion, or electromagnetic interference, polling delays accumulate. A detector that should respond within 8 seconds may take 20–35 seconds during loop communication degradation.
For facilities where cause-and-effect logic triggers suppression systems or evacuation, this delay can be catastrophic. Loop communication quality should be measured continuously, not assumed.
3. Ground Fault Problems
Ground faults occur when circuit conductors make unintended contact with earth or grounded conductors. In fire alarm wiring, this manifests as an insulation breakdown between cable conductors and conduit, structural metalwork, or damp surfaces. A partial ground fault degrades signal integrity across the entire loop. A full ground fault can take an addressable loop offline.
Ground faults are insidious because they often fluctuate with temperature and humidity, appearing intermittently and resisting localisation during inspections.
4. Ageing Detection Devices
Smoke detectors have a defined service life, typically 8–12 years for ionisation detectors and 10–15 years for photoelectric devices. As detectors age, their sensing chambers accumulate contamination, their optical components lose efficiency, and their internal reference circuits drift from calibration. Ageing detectors are more prone to false alarms and more likely to miss low-density smoke events.
Many facilities run detectors well beyond their design life, particularly in areas perceived as low-risk. This is a common source of hidden instability in educational campuses and older commercial towers.
5. Dust Contamination in Detectors
Photoelectric smoke detectors work by detecting light scatter from particles entering the sensing chamber. When dust accumulates inside the chamber, it creates a persistent scatter effect that either elevates sensitivity (causing false alarms) or compensates by reducing gain (causing missed detections). Both outcomes represent instability.
In warehouses, manufacturing facilities, and distribution centres, where airborne particulates are elevated, dust contamination accelerates detector performance drift significantly faster than in clean environments.
6. Improper Detector Placement
Detector placement that was adequate at commissioning may become inappropriate as facility layouts change. Additions of shelving, machinery, suspended ceilings, HVAC modifications, or airflow redirections can create dead zones where smoke accumulates before reaching detector coverage areas.
This is a chronic problem in facilities that undergo operational changes without notifying their fire system integrators. The detectors function perfectly, but they no longer cover the hazard geometry effectively.
7. Networked Panel Communication Delays
Large facilities and campus-wide installations use networked fire alarm panels that must communicate with each other to execute site-wide cause-and-effect logic. When network infrastructure introduces latency due to switch congestion, cable faults, or IP configuration errors, panel-to-panel communication degrades.
In a hospital with 15 networked panels, a communication delay of even 3–5 seconds between remote and master panels can prevent coordinated evacuation logic from executing correctly during a real event.
8. Battery Degradation
Sealed lead-acid and lithium standby batteries in fire alarm systems lose capacity progressively. After 3–5 years of charge cycling, most batteries retain only 60–80% of their rated capacity. Under extended power outage conditions, degraded batteries may fail to sustain the panel and devices for the code-required standby duration.
Battery degradation is rarely visible externally. Without capacity testing, it is impossible to know whether standby power will hold for 24 or 72 hours as required.
9. Thermal Stress on Control Panels
Fire alarm control panels generate heat during operation, and they must dissipate that heat effectively. When installed in enclosed mechanical rooms, poorly ventilated cabinets, or environments with elevated ambient temperatures, panels experience sustained thermal stress that accelerates component ageing, particularly capacitors, relays, and voltage regulators.
Thermal stress also causes micro-cracking in solder joints on printed circuit boards, leading to intermittent electrical connections that are extremely difficult to diagnose.
10. Environmental Interference
Radiofrequency interference from industrial radio equipment, variable frequency drives (VFDs), and wireless communication infrastructure can disrupt addressable loop signals. In data centres and telecommunications facilities, high-density RF environments are common and represent a significant source of unexplained communication anomalies in fire detection systems.
11. Firmware Inconsistencies
In large addressable systems with hundreds of devices, firmware updates are deployed progressively. When different devices or panels run different firmware versions, communication protocol mismatches can occur. These manifest as polling errors, event log inconsistencies, or incorrect cause-and-effect execution.
Firmware inconsistency is particularly problematic in networked systems where panels from a manufacturer’s different product generations must interoperate. This is a common but rarely discussed source of instability in complex fire infrastructure.
12. Poor Device Calibration
Heat detectors, multi-criteria detectors, and aspirating smoke detection systems require periodic calibration verification. When calibration drifts as it inevitably does over time, the detection threshold shifts away from its certified value. This can result in either over-sensitivity (nuisance alarms) or under-sensitivity (missed detections).
Calibration drift is not a system fault. It does not generate error codes. It simply means the detector no longer performs as its certification assumes.
13. False Alarm Sensitivity Drift
Some fire alarm control panels use adaptive algorithms that automatically adjust detector sensitivity in response to environmental changes. While this feature reduces nuisance alarms, it can mask genuine sensitivity degradation by compensating for it. The system appears stable, but the compensation margin is gradually consumed until the detector can no longer be compensated.
14. Integration Instability with BMS Systems
Modern fire detection systems integrate with Building Management Systems (BMS) via BACnet, Modbus, or proprietary protocols. When BMS software updates, server replacements, or IP address changes occur without corresponding updates to fire system integration mappings, cause-and-effect outputs fail silently.
A fire that triggers elevator recall, HVAC shutdown, and pressurisation sequences relies on intact BMS integration. Integration instability means these life-safety sequences may not execute correctly.
15. Wiring Integrity Problems
Fire alarm wiring, particularly in older installations, is subject to insulation ageing, mechanical damage from building modifications, and connection oxidation at terminal blocks. High-resistance joints in loop wiring reduce signal quality without generating obvious fault codes. Over time, these micro-resistance increases accumulate until communication reliability drops below functional thresholds.
16. Moisture and Corrosion Effects
In coastal environments, facilities near chemical processes, underground installations, and buildings with HVAC condensation issues, moisture infiltrates detector housings and terminal enclosures. Moisture accelerates copper corrosion on wiring terminals, causes printed circuit board oxidation, and promotes mould growth inside detector chambers, all of which degrade performance invisibly.
How Hidden Instability Affects Fire Detection Performance
The downstream consequences of hidden instability extend across every dimension of fire system operation:
Detection Accuracy and Alarm Response Time
The primary function of a fire detection system is to identify a fire quickly and accurately. Hidden instability degrades both speed and accuracy. A detector operating with dust contamination or sensitivity drift may detect a fire 30–120 seconds later than a calibrated device. In a fast-developing fire, this delay can mean the difference between successful suppression and structural loss.
Evacuation Reliability
Delays in detection cascade directly into delayed evacuation initiation. For facilities with high occupancy hospitals, airports, commercial towers, and educational campuses, every additional minute before alarm activation increases evacuation difficulty and risk. Unstable networked panels may also fail to activate voice evacuation systems in the correct sequence, causing confusion and counter-flow.
Firefighter Coordination
Emergency services rely on fire alarm panel outputs, remote annunciator displays, and building control room information to locate fires and direct suppression efforts. Inaccurate panel data caused by addressable system loop delays or BMS integration failures misdirects firefighting resources and extends suppression time.
Compliance Inspections and Legal Liability
Regulatory compliance for fire detection systems is not a point-in-time certification. It is a continuous operational requirement. A system with hidden instability that fails during a fire event, even if it passed its last inspection, creates profound legal and regulatory liability for building owners, facility managers, and system maintainers.
Cause-and-Effect Logic Execution
Modern fire systems execute complex cause-and-effect sequences: detector activation triggers HVAC shutdown, elevator recall, stairwell pressurisation, suppression release, and emergency communication. When communication delays, BMS integration failures, or firmware inconsistencies disrupt this logic, safety-critical sequences fail silently. The fire alarm sounds, but the building does not respond as designed.
Real-World Examples Across Facility Types
Data Centres
A Tier III data centre in Southeast Asia experienced repeated nuisance alarms from aspirating smoke detection systems. Investigation revealed that server airflow modifications had changed smoke transport patterns, causing the detection system to trigger on recirculated particulates rather than actual combustion products. The system was technically functional, but its placement was no longer valid for the modified environment.
Hospitals
A regional hospital’s fire alarm system was found during a diagnostic audit to have 23 detectors operating on firmware versions three generations behind the control panel. The incompatibility caused a 4-second polling delay on those zones, enough to potentially delay activation of the operating theatre’s local suppression system during a critical cauterisation fire event.
Industrial Plants
A petrochemical facility discovered during a loop resistance survey that seven cable sections had developed high-resistance joints due to terminal corrosion in a high-humidity area. The addressable loop showed no fault codes, but loop communication quality had degraded by 40% in those zones enough to cause intermittent device polling failures during temperature extremes.
Airports
A major international airport’s fire alarm network spanning 14 buildings and 22 networked panels was found during a system audit to have three panel-to-panel network segments operating at 65% communication efficiency due to ageing network switches. Cause-and-effect logic for airside evacuation depended on inter-panel communication completing within 2 seconds. The degraded network was taking 6–8 seconds, a condition that had existed undetected for approximately 18 months.
Commercial Towers
In a 42-story commercial tower, a systematic battery capacity test revealed that 31% of standby batteries were below 70% of rated capacity, sufficient for short power outages but unable to sustain the 24-hour standby requirement mandated by code. None of these batteries had triggered a fault code; they simply had insufficient capacity for extended emergency operation.
Warning Signs Your Fire Detection Infrastructure Is Becoming Unstable
Recognising early indicators of instability allows engineering teams to intervene before performance deteriorates to critical levels. The following are the most operationally significant warning signs:
- Increasing frequency of nuisance alarms, even if individually explainable.
- Detectors or zones appear intermittently on the panel event log without generating persistent faults.
- Loop communication quality scores are declining on addressable panel diagnostics.
- Unexplained panel restarts or spontaneous configuration reloads.
- Standby battery test duration shorter than the rated capacity would predict.
- BMS integration outputs are not reflecting the fire system status within the expected timeframes.
- Growing volume of unacknowledged or auto-cleared events in the system log.
- Detectors requiring repeated cleaning with sensitivity still below baseline.
- Firmware version mismatches were identified during system audits.
- Ground fault indicators appear intermittently during temperature changes.
- Elevated loop resistance readings compared to the commissioning baseline.
- Increase in response time variance during functional testing.
How to Audit and Diagnose Hidden Fire System Instability
A comprehensive fire system instability audit goes well beyond standard functional testing. It involves quantitative measurement of system performance parameters and comparison against commissioning baselines and design specifications.
Step 1: Establish or Recover Commissioning Baselines
Every measurement of current performance requires a reference point. Retrieve original commissioning data for loop resistance, insulation resistance, battery capacity, and detector sensitivity settings. If baselines do not exist, create them during the audit as a starting point for future trend analysis.
Step 2: Perform Loop Resistance and Insulation Testing
Using a calibrated loop resistance meter and insulation resistance tester (500V DC), measure resistance and insulation quality on every loop segment. Compare against baseline and flag any segment showing resistance increases greater than 10% or insulation resistance below 1 MOhm.
Step 3: Conduct Battery Capacity Testing
Replace simple voltage checks with actual load-based capacity tests. Apply a discharge load equivalent to full system current draw and measure discharge duration. Replace any battery that cannot sustain the rated standby duration minus a 25% safety margin.
Step 4: Analyse Panel Event Logs
Download and analyse the complete panel event log for the previous 12 months. Look for patterns: zones that generate disproportionate events, time-correlated faults, devices with repeated auto-restore messages, and communication error clusters. These patterns reveal instability invisible to standard inspection.
Step 5: Verify Firmware Consistency
Generate a firmware inventory across all addressable devices and panels. Identify version mismatches and consult the manufacturer’s compatibility matrix to assess whether identified combinations have known interoperability issues.
Step 6: Test BMS Integration Under Simulated Conditions
Execute cause-and-effect scenarios with BMS monitoring active and measure the delay between fire panel output and BMS response for each programmed integration sequence. Document and compare against design specifications.
Step 7: Verify Detector Sensitivity and Placement
Using a detector sensitivity meter, test each addressable detector for its actual sensitivity value and compare it against the panel-programmed threshold. Simultaneously review detector placement against current floor plans and airflow surveys to identify any coverage gaps created by facility modifications.
Best Practices to Improve Fire Detection Stability
- Deploy addressable fire alarm panels with full loop supervision for all new and refurbished installations. They provide real-time diagnostic insight that conventional panels cannot match.
- Implement continuous power quality monitoring at fire alarm panel supply circuits in high-risk facilities.
- Establish firmware management protocols that ensure version consistency across all networked devices and panels following any system update.
- Schedule battery capacity tests, not voltage checks, on an annual or biannual basis, depending on battery age and service environment.
- Integrate GST fire alarm system diagnostics data with CMMS (Computerised Maintenance Management Systems) to enable trend-based maintenance planning.
- Deploy addressable detectors with built-in sensitivity reporting and automatic drift compensation in dusty or contaminated environments.
- Conduct full loop resistance surveys as part of every annual inspection, not as a standalone activity.
- Review and revalidate BMS integration outputs after any BMS software update, server migration, or IP infrastructure change.
- Implement a detector lifecycle management program that proactively replaces devices approaching the end of their rated service life.
- In networked systems, deploy managed network switches with SNMP monitoring to detect communication quality degradation before it becomes a loop failure.
- Establish a minimum inspection frequency for facilities in corrosive, humid, or high-particulate environments, typically quarterly rather than annually.
- For mission-critical facilities, consider cloud-connected fire system supervision platforms that provide continuous, remote monitoring of system health parameters.
Performance Comparison: Stable vs. Poorly Maintained Fire Detection Infrastructure
The following table illustrates the operational performance gap between a well-maintained intelligent fire detection system and one affected by hidden instability:
| Parameter | Stable Intelligent System | Poorly Maintained System |
| Detection Response Time | < 10 seconds (addressable) | 30–90 seconds or more |
| False Alarm Rate | < 1% annually | 10–25% annually |
| System Uptime | > 99.9% | 85–95% (unexpected faults) |
| Loop Communication | Continuous, error-free polling | Intermittent, packet loss |
| Battery Health | Monitored, replaced proactively | Unknown, failure risk |
| Detector Calibration | Auto-calibrated or tested regularly | Drift undetected for years |
| Ground Fault Visibility | Instant panel alert | Undetected until a major fault |
| Firmware Status | Unified, current across all nodes | Mixed versions, conflicts |
| BMS Integration | Seamless, tested | Unreliable, time-lagged |
| Compliance Readiness | Pass-ready at all times | High risk of citation/failure |
| Maintenance Model | Predictive, scheduled | Reactive, breakdown-driven |
| Dust/Contamination | Alerts triggered by sensitivity drift | Undetected until failure |
| Wiring Integrity | Supervised continuously | Periodic manual check only |
| Cybersecurity Posture | Encrypted, segmented networks | Open, unpatched vulnerabilities |
The Future of Fire Detection: Intelligent Infrastructure and Predictive Stability
The next generation of fire detection technology is moving decisively toward continuous health monitoring, AI-assisted diagnostics, and predictive maintenance, shifting the paradigm from ‘respond to failures’ to ‘prevent them from occurring.’
AI-Assisted Fire System Diagnostics
Artificial intelligence platforms can analyse addressable fire alarm panel event logs, loop communication quality data, and detector performance metrics to identify instability patterns long before they produce detectable faults. By correlating thousands of micro-events, each individually insignificant, AI diagnostic systems can predict device failures, communication degradation, and sensitivity drift weeks in advance.
Predictive Maintenance Platforms
Cloud-connected fire detection systems with predictive maintenance integration generate automated maintenance work orders based on performance trend analysis. Rather than replacing components on a fixed schedule, predictive platforms replace them based on actual measured conditions, reducing cost while improving reliability.
Smart Detector Health Monitoring
Modern addressable detectors incorporate internal health monitoring that continuously reports sensing chamber contamination levels, optical efficiency, and temperature compensation status. When paired with a system that analyses this data centrally, facilities gain real-time visibility into detector health across the entire installation.
Digital Twins for Fire Infrastructure
Digital twin technology allows fire protection engineers to model fire detection infrastructure virtually, simulating performance under different facility configurations, fire scenarios, and degradation states. Digital twins enable engineers to test system modifications, evaluate detection coverage for planned facility changes, and model the impact of component ageing, all without physical intervention.
Cybersecurity in Connected Fire Alarm Networks
As fire detection systems become increasingly networked, connecting to BMS, cloud platforms, and enterprise management systems, cybersecurity becomes a fire safety consideration. Unauthorised access to a fire alarm network could allow system manipulation, false alarm generation, or suppression of genuine alarms. Best practice requires network segmentation, encrypted communication, role-based access control, and regular security audit of the fire system network infrastructure.
Self-Diagnostic Addressable Systems
The latest generation of addressable fire alarm systems incorporates self-diagnostic capabilities that continuously assess loop communication quality, device health, power supply performance, and firmware integrity, generating structured health reports without manual intervention. These platforms represent the practical implementation of condition-based maintenance for fire infrastructure.
Read Also: Why Fire Alarm Systems Need Context-Aware Event Logic in Modern Facilities
Read Also: Why Advanced Fire Alarm Systems Still Fail in Real Scenarios